
“Header From” spoofing is a common email impersonation tactic where a malicious actor forges the visible “From” address of an email to appear as a legitimate sender. While the email seems to be from a trusted source, the true origin is from a different, often deceptive, domain. This technique relies on tricking the recipient, as the average user can’t easily see the discrepancy between the forged visible address and the email’s true source.
To better understand this attack, let’s explore a hypothetical scenario involving a company like google.com.
How the Attack Works
A “Header From” spoofing attack is a multi-step process designed to bypass basic email security checks and deceive recipients.

STEP 1
Register a Lookalike Domain: The attacker first registers a domain that closely resembles the legitimate one, such as googlee.com (with an extra ‘e’) or another similar variation.

STEP 2
Set Up a Valid SPF Record: To avoid being flagged as spam by email servers, the attacker sets up a valid Sender Policy Framework (SPF) record for the newly registered decoy domain. This SPF record authorizes the sending server, allowing the email to pass basic server-level checks.

STEP 3
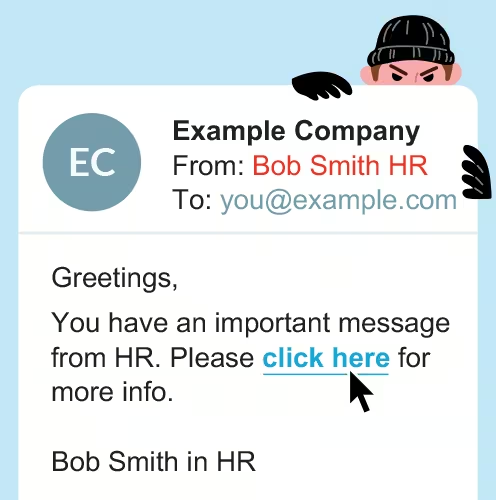
Forge the “Header From” Address: The attacker then changes the visible “From” address to an employee’s real name and email address from the target company (e.g., from [email protected] to Bob Smith HR or even [email protected]).
STEP 4
Send the Impersonating Email: An email is sent to an unsuspecting user, appearing to be from the legitimate employee.

STEP 5
Extract Information: The user, believing the email is authentic, responds to a request for sensitive information, data, or resources, which is then collected by the attacker.

NOTE
Although the visible “Header From” address is forged, the hidden “Envelope From” address still reflects the decoy domain (googlee.com). Users can’t see this discrepancy, but security protocols like DMARC can.
How DMARC Protects Against Spoofing
Domain-based Message Authentication, Reporting, and Conformance (DMARC) is a powerful email authentication protocol that helps prevent “Header From” spoofing. It works by verifying that the domain in the “Header From” address aligns with the domain in the “Envelope From” address. What happens when this alignment fails depends on the company’s DMARC policy.
| Policy | p=none | p-reject |
|---|---|---|
| User Risk | ❌ High Risk | ✅ Protected |
| Mechanism | This policy lets the email through. When DMARC detects the domain mismatch, it doesn’t take action. It simply monitors and reports the issue without blocking delivery. | This policy blocks the spoofing email. Once DMARC detects the misalignment, the email server immediately rejects the message, and a bounce-back error is sent to the attacker. |
| Outcome | The email’s final location is unpredictable; it could end up in the user’s inbox, spam folder, or be filtered by other systems. | You and the attacker both know the spoofing attempt was unsuccessful, and the target user never sees the email. |
Ultimately, a p=none policy puts the user at risk because it lacks a mechanism to stop the email, while a p=reject policy protects the user by preventing the spoofed email from ever reaching its destination.
The Challenge of DMARC Implementation
While the benefits of a strict DMARC policy like p=reject are clear, getting there can be a complex journey. Many organizations start with a p=none policy, which is a crucial first step for monitoring. This policy allows you to gather valuable data on who is sending emails on behalf of your domain, both legitimate and illegitimate. The challenge lies in analyzing this data to identify all your authorized senders—like marketing platforms, HR systems, and other third-party services—and ensuring they are correctly configured.
Misconfiguring these legitimate senders can lead to a major problem: your own emails getting blocked once you switch to a stricter policy. The process of analyzing DMARC reports, identifying all your sending sources, and moving safely to a p=reject policy requires specialized knowledge and can be a significant undertaking for any IT or security team. Without the right tools, this process is manual, time-consuming, and prone to errors.
The Solution: A Smarter Way to Manage DMARC
This is where a dedicated DMARC management platform becomes essential. Instead of manually sifting through complex DMARC reports and risking a misstep that could disrupt your business communications, a product like OnDMARC simplifies the entire process. OnDMARC provides a clear, actionable view of your email ecosystem, showing you exactly who is sending emails on your behalf and whether they are correctly authenticated.
With features designed for effortless implementation, OnDMARC guides you from p=none to p=reject with confidence. It helps you identify all legitimate email sources, correct authentication issues, and monitor for malicious activity in real-time. By automating the complexities of DMARC, OnDMARC ensures your domain is protected from spoofing attacks, securing your brand and your customers from a growing threat.
Need Help With Your DMARC Setup?
Learn more about 101domain’s Managed DMARC Services and let us do the heavy lifting for you. We handle policy setup, monitoring, and reporting so you can rest easy knowing your emails are secure.
